Myra V.rar Apr 2026
Cybercriminals often use generic or enticing names (like "Leaked_Photos.rar" or "Person_Name.rar") to trick users into downloading and executing malicious scripts, such as trojans or ransomware .
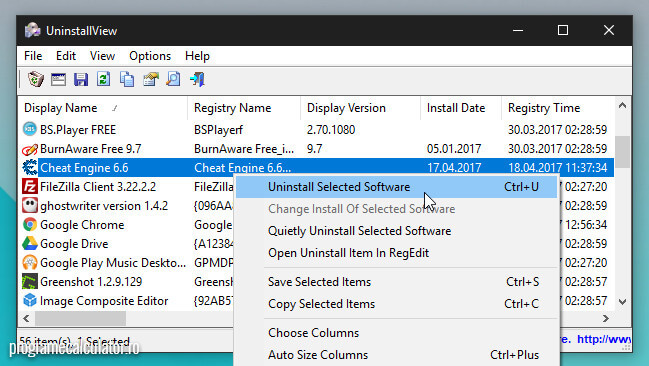
Right-click the file and check "Properties" to see the creation date or origin, which might provide a clue to its purpose. Myra V.rar
Recall where the file originated. If it arrived via an unsolicited email, a suspicious social media link, or a "cracked" software site, it is highly likely to be malicious . Cybercriminals often use generic or enticing names (like
If you plan to interact with this file, follow these industry-standard security protocols: a suspicious social media link