Ian18.rar -
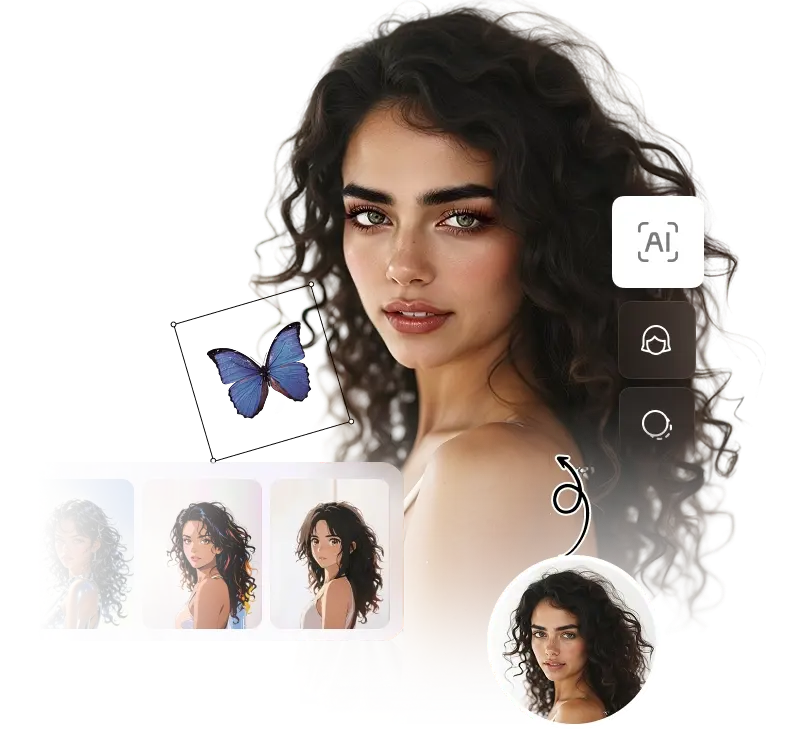
Meitu is the All-in-one photo and video free editor on mobile, which gives you everything you need to create awesome edits.
Download Now

The file is likely associated with the Flare-On CTF 2018 (specifically Challenge 10) or a similar forensic/reverse engineering challenge. In the context of CTFs (Capture The Flag), a "write-up" is a guide explaining how a challenge was solved. Write-up Summary for Challenge 10 (IAN18)
Challenge 10 of the 2018 Flare-On competition involved an image file and a deeply obfuscated sequence. Below is the general methodology for tackling such a challenge:
Extracting a hidden payload from the metadata of an image or within the RAR's comment field.
: Challenges of this level typically include a binary (like an .exe or .dll ) inside the archive. You would use a disassembler like IDA Pro or Ghidra to reverse the code.
The file is likely associated with the Flare-On CTF 2018 (specifically Challenge 10) or a similar forensic/reverse engineering challenge. In the context of CTFs (Capture The Flag), a "write-up" is a guide explaining how a challenge was solved. Write-up Summary for Challenge 10 (IAN18)
Challenge 10 of the 2018 Flare-On competition involved an image file and a deeply obfuscated sequence. Below is the general methodology for tackling such a challenge: IAN18.rar
Extracting a hidden payload from the metadata of an image or within the RAR's comment field. The file is likely associated with the Flare-On
: Challenges of this level typically include a binary (like an .exe or .dll ) inside the archive. You would use a disassembler like IDA Pro or Ghidra to reverse the code. IAN18.rar