File: Midnightsnack-2022-08-02.7z ... Site
: Usually traced back to a phishing email leading to a "ISO" or "LNK" file masquerading as a document.
The file is associated with a digital forensics and incident response (DFIR) challenge , typically found on platforms like CyberDefenders . The challenge involves analyzing a memory dump to identify malicious activity on a compromised workstation. Analysis Summary File: MidnightSnack-2022-08-02.7z ...
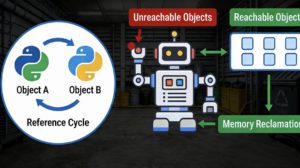
: An endpoint was compromised after a user downloaded a suspicious file. The goal is to trace the execution flow, identify the malware family, and locate the Command and Control (C2) infrastructure. : Usually traced back to a phishing email
: The "MidnightSnack" moniker often refers to a specific stealer or backdoor that activates during low-user-activity hours to exfiltrate sensitive browser data, cookies, or credentials. Common Findings identify the malware family